LSOF: How to List Open Files in Unix Systems
What is LSOF?
The LSOF command, which stands for "LiSt Open Files," is a...
Introduction to Chmod Recursive
For users of Unix and Linux operating systems, managing file permissions is a vital aspect of system...
Enable SSH Ubuntu: How to Securely Access your Remote Server
Learning how to enable SSH (Secure Shell) on Ubuntu is a crucial step...
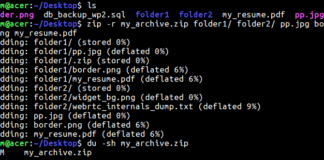
How to Compress Files Using the Linux Zip Command
The Linux zip command is an essential tool for file compression and archiving in Unix-based systems. Whether...
Ubuntu Server GUI: Installing and Managing a Graphical Interface
The Ubuntu Server is famous for command-line interface, optimized for performance and efficiency. However, there are situations...
Navigating Cybersecurity Threats with Linux and Anonymity Tools
Despite the numerous benefits and advantages, we get from the Internet and Information Technologies (IT), the connectivity...
Leveraging Linux/Unix for Preventing Repeat Signups in E-commerce
E-commerce websites face a range of challenges, from managing inventory to ensuring secure transactions. One often-overlooked issue...
Elementor Website Design Templates: Jumpstart Your Creative Process
Do you want the Elementor website design templates? Which things should you notice in the website designer...
Crash Course on Organizing Your Workday on Linux
Crash Course on Organizing Your Workday on Linux
As a Linux distribution user,...
Unlock the Power Reverse Email Lookup With Linux: Improving Security and...
Email is a major communication mode in today’s digital era. Whether you use it for personal interactions,...
Curl command mastery: A complete guide
Curl command was first developed by a developer who wanted to get foreign exchange rates of his...
[Solved] – How to Fix SSH Permission Denied (Publickey) Error Message
You want to apply a critical patch on your Linux servers. This has been done many times...
How Threat Intelligence Reduces Cybercrime
Companies that perform most of their operations online risk being attacked by cybercriminals trying to steal their...
The Role of Outsourcing in Web Development for Linux Software Solutions
Outsourcing web development plays a pivotal role in successfully executing Linux software solutions. How to outsource web...
Best Practices for Securing Office 365 On Linux
Most organizations use Microsoft Office 365 to team up on projects and share files. It is officially...
Distrobox: Manage Your Linux Distros Like a Pro
Introduction
Are you are a Linux user with multiple distributions but hates the hassle...
A Guide on How to Master Bash If Else… Statements
Introduction
As someone who creates apps and occasionally uses Linux, it's crucial to control...
How to Fix the SSH Permission Denied (publickey) Error
Introduction
SSH, or Secure Shell, is an essential protocol that is widely-used in the...











![[Solved] – How to Fix SSH Permission Denied (Publickey) Error Message how to fix ssh permission denied publickey error](https://www.unixmen.com/wp-content/uploads/2024/06/how-to-fix-ssh-permission-denied-publickey-error-324x160.png)








